A Pedophile Hunter Tells Mommyish How He Takes Down Child Pornography Rings
One of the reasons I started closely following the actions of Anonymous is because one of their main objectives at any given moment is putting a stop to child porn and the exploitation of children on the Internet. In October of 2011, they put Operation Darknet into action and took down an insidious website called “Lolita City”, where users could exchange child pornography. [youtube_iframe id=”rah535JmEI8″]
Anonymous members and sects continue to hunt child predators on the Internet, and I spoke with one member who has made putting an end to child pornography his life’s work.
How did you learn to find predators on the internet? You work through various social media websites, online games, and regular websites?
Basically, we are all over the Internet. Websites, online games, chat rooms, social media such as Twitter. I am self taught, however I am constantly learning new things everyday thanks to the amazing people I am surrounded by and interact with online. I will not mention them but they know who they are. One person in particular started this operation and then handed it me. He was a great role model and a inspiration. In my spare time I come online and hunt pedophiles and predators with a group of amazing people. I started hunting predators because I personally believed enough was not being done to protect children online by law enforcement I still believe it. Government and law enforcement are to concerned with arresting whistle-blowers and hacktavists and seem to let everyone else off lightly.
(*Editor’s note: The amount of time varies by case, but a general estimation of the amount of prison time sentenced to computer hackers is 50 years. For someone who distributes child pornography the sentence is 20 years.)
Can you name any websites that parents need to be super cautious of their children visiting?
A popular website a lot of parents may be familiar with is Habbo Hotel, that you can also play on Facebook. It’s basically a haven for pedophiles. In the past we have experienced many pedophiles on here. Although no pictures or videos can be swapped they like to exchange email address’s which opens up a lot more possibilities for them. That’s how the predators target children. As with most sites that cannot display pictures, they aim of predators is to exchange email address’s. That way they can exchange pictures and potentially groom unsuspecting victims. This site is no different from any other role playing game. It was simply the amount of people engaging in this sort of activity on the site that drew our attention to it. In my opinion, sites do try and protect people’s information. As always there is always more that can be done though. Unfortunately as more security measures are introduced more loopholes are also. The most common method sites use is filtering and blocking email addresses. This is very basic and simple to get around as all predators know. Because of this I personally do not think it a deterrent to predators.
How do you take down websites?
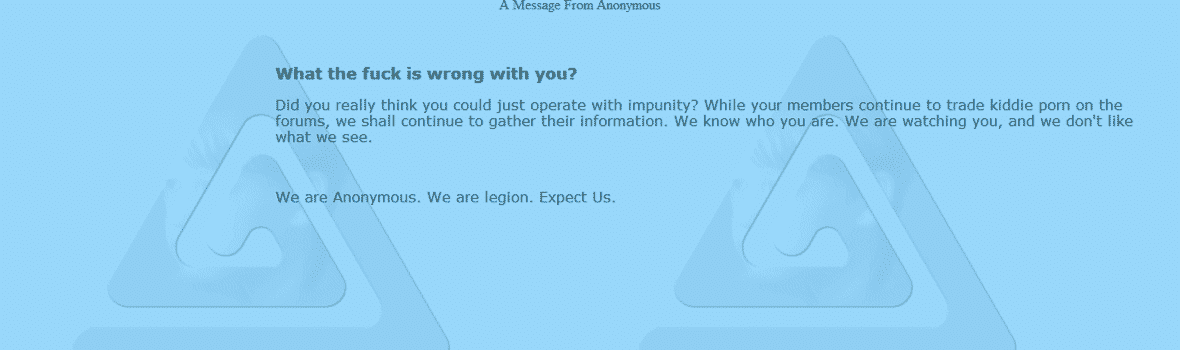
With a variety of methods. There is the legal way, which involves collecting evidence and reporting it to the host and correct authorities. Then there is the means by which we are more commonly associated. The method commonly used is to DDoS (Distributed denial of service) a site. A good analogy of this is to think of a call center. Say it has 50 phones. What happens is 50 requests (phone calls) are made to each phone, making it unavailable to actual customers or people that want to get through. It is just flooding the site so others cannot access it. Also, if the site has a vulnerability you might see something else happening to it, such as a database leak, or a common deface, which looks like this:
So, after this you contact local law enforcement. What happens then?
We do a lot more. In fact reporting to law enforcement is one of the last steps we take. When a pedophile browses a forum/website or conducts illegal activities online, such as viewing child porn, for obvious reasons they do not use their real names or information. This is our first challenge. At this point we look into each individual and put together a “DOX” (basically the persons information, it can range from a basic name and address and phone number to social security numbers etc..)
After that initial step, we look into the person further, see if they are connected to any other sites to gain evidence and to see if they are linked to a group. When that is done, then we contact law enforcement. Unfortunately we can not obtain what percentage of these reports lead to further action. If we find that the above fails, we do not simply give up. Depending on the scenario we may choose to try and social engineer the person(s) into giving out information about other websites, etc. For obvious reasons, myself or others can not explain every method. The ones mentioned are the basic steps.
How many websites and Twitter accounts are reported to you daily?
It varies due to obvious reasons, however on a “average” day we have at least 10 social media handles reported to us. Some days it can peak at around 50-60 accounts if a pedophile ring has been discovered. As for websites, not as many. We generally only have one or two reported which is a good sign in my eyes, although the majority of the sites that we target are found by members working on this Operation.
What do you think parents aren’t aware of and what security precautions should we be taking?
I think parents are not aware of the things they should look out for and trust is a key issue. If your child can speak to you about their problems, they have no need to speak to a stranger about it online. Although in some cases no matter what you do it might not still be enough. If you have settings in place, then use them. It will minimize the risk. Most computers have parental settings for a reason. They can be a massive help. Use them. Also, if it is a particular site that is causing concern, block it via your router.
One last thing, If you think your child is too computer smart for you, we are here to help. Do not be afraid to ask us questions. Just because they have deleted their Internet history, does not mean you can not see what they have been on.
How does doing this work and participating in stopping child porn effect you personally?
It effects me greatly. You can never “un-see” images. It haunts you. It makes you lose faith in humanity. As always people are effected in different ways. The majority of people that work on this Op have lost sleep over what they have seen and have no doubt vomited and cried. Some of us start drinking or drink more, others turn to smoking pot. Obviously I can’t speak for anyone else. This is just from personal experience and what I use on bad days. Drugs and alcohol is not the way to deal with problems. It will solve nothing in the long run. Communication is key, thanks to all those that I can talk to. That is the reason I would personally like to say a huge thank you to all that have ever worked on these operations, are currently working on this Op or that in the future will help. You are heroes in my eyes. Also a massive thank you to all that support us. We would still do what we do without the support but it sure helps with motivation.
Parents, you all do an amazing job and if you ever need advice or questions answered no matter what it is about, we are here to help. Believe it or not but we are not “bad” people. Trust and communication is paramount. Do not give your kids a reason to want to hibernate and express themselves to a total stranger.
Although not everyone on the Internet is bad, predators are out there. Another thing annoying me lately is the number of cases I see where parents try and pit themselves against each other, especially after an ugly divorce where child custody is involved. We see a lot of false allegations of child porn and endangerment in these cases, and it distracts from cases where children are actually being victimized. Parents shouldn’t do that to their kids, and even after a breakup the children should always come first. Try and get along as civilly as possible for the children’s sake.
The operation we are currently working on is going to be going on for a while. The sole purpose is to rid the internet of predators and child porn. If you happen to stumble across a site, a person who may be engaging in harming children, or you are just generally concerned we are to help. If we cannot, we will put you in contact with people that can. We also know a lot of charities if you need contact information for them.
To predators, by now you should know who we are and what we are about. If you don’t, you soon will. Google us, be afraid of us and please, expect us.
We are Anonymous
We are Legion
We do not forgive
We do not forget
Expect us.
You can follow the work of @OpPedoChat on Twitter.